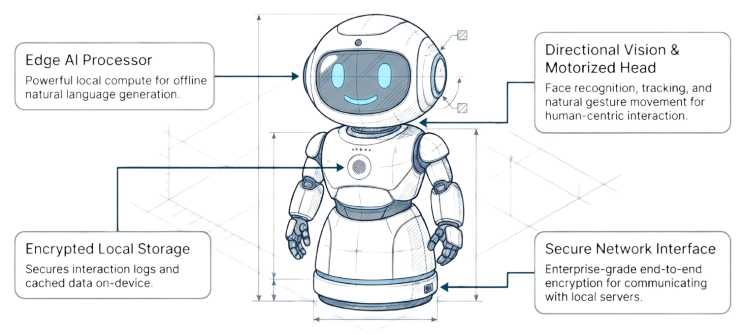
AI Desk Robot Interface
Natural, voice-first interaction with a physical endpoint designed for frontline and command environments.
Process Overview
A quick process map of how requests travel through secure capture, private processing, controlled retrieval, and governed response in TRUCON deployments.
TRUCON PROCESS DIAGRAM
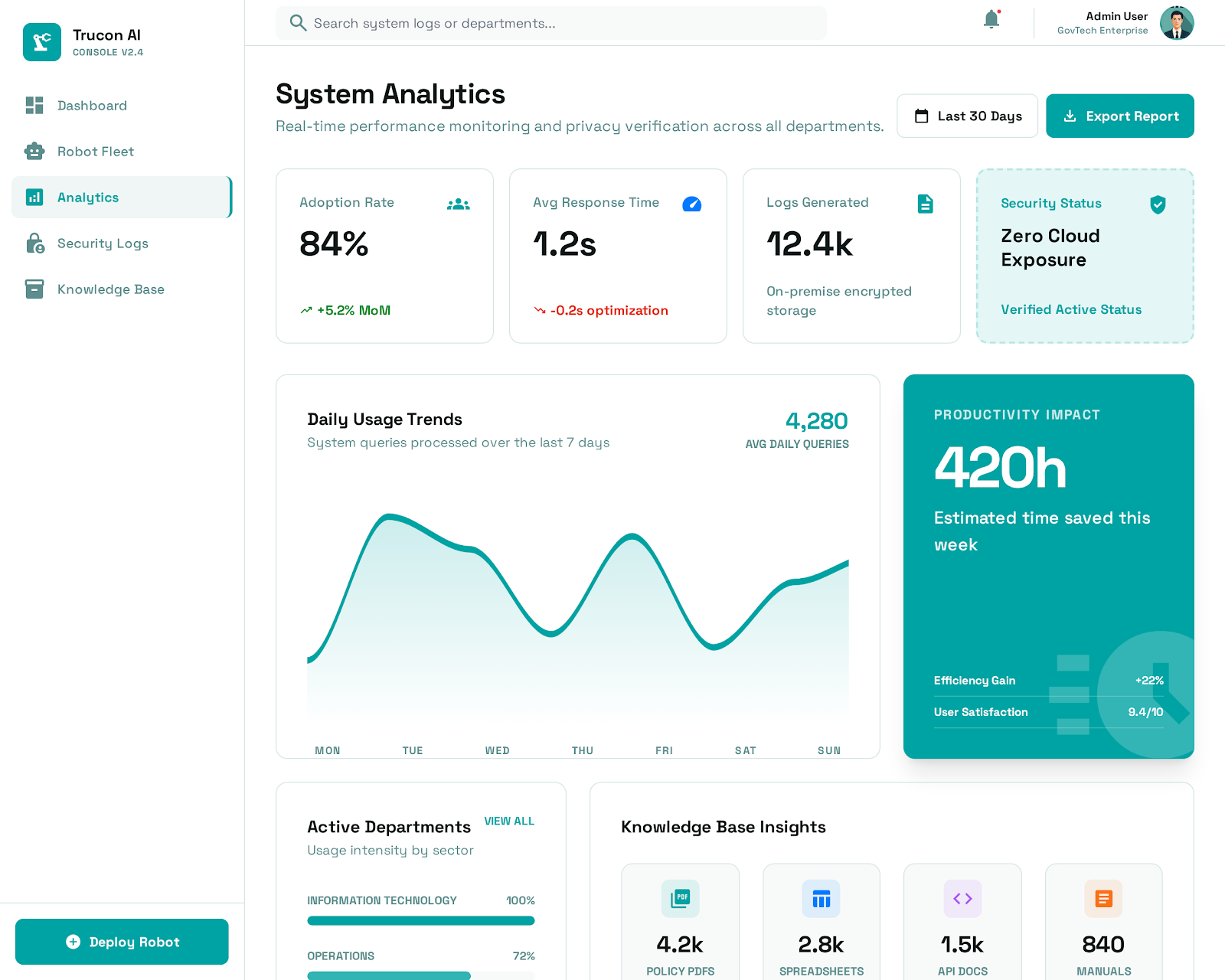
100%
Private Inference Paths
0
Mandatory Cloud Dependency
24/7
Governed Audit Visibility
Designed as modular blocks so organizations can deploy incrementally while preserving security controls and governance standards.
Natural, voice-first interaction with a physical endpoint designed for frontline and command environments.
Inference and orchestration stay within approved enterprise boundaries without cloud prompt leakage.
Secure retrieval, summarization, and contextual answer generation across internal policies and SOPs.
Operational mode support for disconnected sites and restricted networks where uptime is mission-critical.
Role-based access, encryption, event auditing, and policy-aligned safety rails across all interactions.
Responses are grounded on approved enterprise data to reduce hallucinations and improve decision confidence.
A visual journey of how TRUCON transforms an authenticated request into a governed, audit-ready response.
Every interaction starts with authenticated user capture and policy checks before requests enter the processing path.


Inference runs on enterprise-controlled compute with retrieval from approved sources only, preserving confidentiality and traceability.


Final responses are policy-screened, audit-linked, and delivered via robot-first UX for frontline reliability.


Deployment Ready
Get a guided feature walkthrough tailored to your workflows, security requirements, and infrastructure constraints.