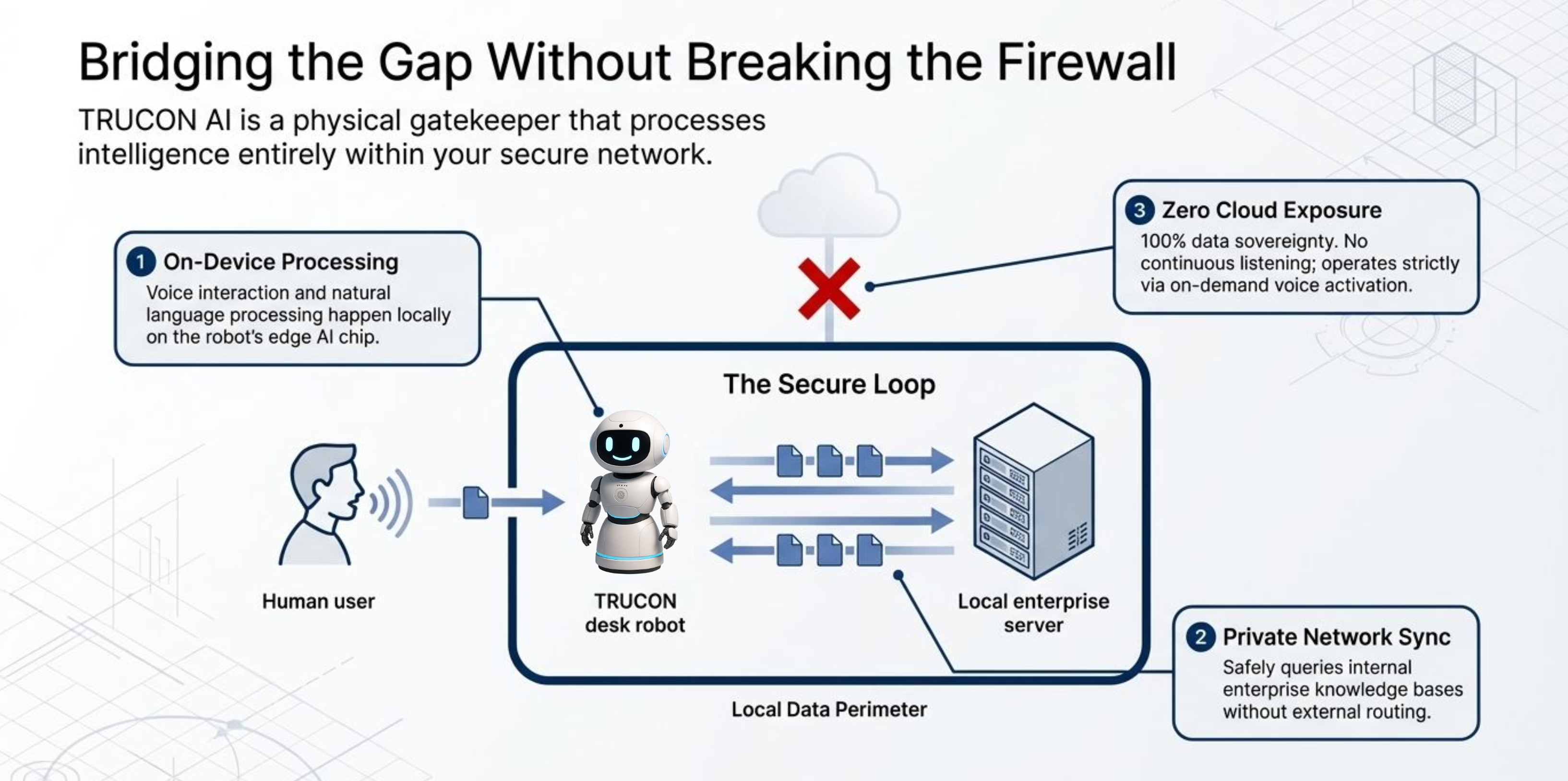
No Cloud Dependency
Core intelligence stays local for secure operations in isolated enterprise and government networks.
Secure, on-device AI assistant designed for government and enterprise environments.
100% safe and compliant • Powered by leading standards • Made in India




Certification under process.
Recognized By Leading Institutions

Rashtriya Raksha University

IIT Gandhinagar
Trust Layer
TRUCON AI is engineered for secure-first environments where ownership, control, and compliance are non-negotiable.
Core intelligence stays local for secure operations in isolated enterprise and government networks.
Voice capture runs only on active interaction, reducing exposure risk in sensitive workspaces.
Organizations retain full control of models, logs, and knowledge with no third-party data sharing.
Role-based controls, encryption, and auditability designed for compliance-driven deployments.
Capabilities
TRUCON AI combines robotics, private LLM intelligence, and secure enterprise integration into one deployable platform.
Human-like interaction through voice, presence awareness, and instant real-time assistance.
All inference and orchestration happen on-device or within private network boundaries.
Search, summarize, and retrieve internal documents with enterprise context and full traceability.
Built-in controls for role-based access, audit logs, policy enforcement, and compliance workflows.
Keep operations running in restricted or disconnected zones without losing assistant capability.
Ask natural language questions against internal systems and get grounded, policy-safe responses.
Use Cases
Purpose-built for operational environments that demand trust, continuity, and compliant intelligence.
Sovereign AI support for policy, citizen services, and secure mission workflows.
Intelligent frontline and back-office assistance inside private corporate environments.
Operational and document intelligence that protects patient-sensitive data boundaries.
Trusted campus intelligence for knowledge retrieval, operations, and student support desks.
Ambient secure AI assistance for modern workplaces with strict infrastructure controls.
Product Showcase
A secure robotics endpoint purpose-built to become the trusted intelligence interface for modern secure workspaces.
Engineered for secure desks, control rooms, and enterprise command environments where every AI interaction must remain private, accountable, and resilient.
Why TRUCON
A platform architecture aligned with security-first enterprises and sovereign public-sector requirements.
| Feature | TRUCON | Cloud AI |
|---|---|---|
| Data Privacy | Yes | No |
| On-device AI | Yes | No |
| Offline Capability | Yes | No |
| Enterprise Ready | Yes | No |
Everything teams usually ask before deploying TRUCON in secure, compliance-driven environments.
TRUCON is built for privacy-first deployments. Core processing stays within approved infrastructure boundaries, with governance controls and audit-ready workflows for high-trust environments.
Share your environment details and we will help you evaluate the best secure deployment path for your team.